- SASE security offers a cloud-based framework that integrates network and security functions, ensuring scalable, efficient, and secure access for distributed workforces and IT environments.
- Core features include secure web gateways, firewalls-as-a-service, and zero trust network access, emphasizing centralized policy control and enhanced user experience.
- The architecture prioritizes isolation and zero trust methodologies to eliminate malware threats, streamline security operations, and support seamless digital transformation.
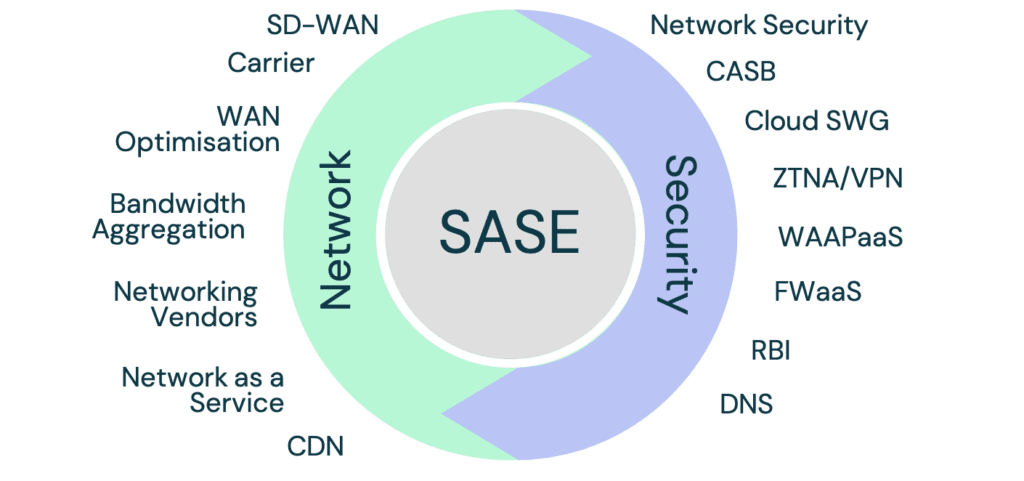
SASE (Secure Access Service Edge) is a security framework designed to address the challenges of modern, distributed IT environments. It integrates network and security functions in the cloud, providing secure, efficient, and scalable access for users, applications, and data regardless of location or device. By moving beyond traditional perimeter-based security models, SASE ensures protection for increasingly remote and hybrid workforces.
Key components of SASE include secure web gateways (SWG), cloud access security brokers (CASB), firewalls-as-a-service (FWaaS), and zero trust network access (ZTNA). These tools operate cohesively within a unified framework to protect users and endpoints, applying consistent policies and enabling centralized management. This integration reduces operational complexity and improves visibility across diverse environments, ensuring a holistic approach to security.
Zero trust methodologies are foundational to SASE, emphasizing continuous verification and limited access to applications and data. This is reinforced by isolation technologies, which prevent malware from reaching endpoints by processing potentially harmful content in a secure, remote environment. Such measures eliminate threats while maintaining seamless user experiences, enabling secure browsing, email usage, and interaction with web applications.
SASE also supports scalability and flexibility, making it suitable for organizations of all sizes. Its cloud-native design improves the user experience by reducing latency and enhancing access performance, especially for cloud-based applications. With its ability to adapt to evolving threats and accommodate growing business needs, SASE is a transformative solution for organizations undergoing digital transformation, ensuring secure, efficient, and resilient operations in a globally distributed environment.


Leave a Reply
You must be logged in to post a comment.