- Biometric authentication emerges as a powerful security measure for businesses to protect sensitive information and valuable assets amidst the growing cyber threats in the digital age.
- The adoption of biometric authentication in business environments is driven by its numerous advantages over traditional authentication methods.
- Implementing biometric authentication systems, however, comes with challenges such as integration with existing infrastructure, user acceptance, cost, and scalability. Despite these hurdles, the benefits of biometric authentication—enhanced security, increased convenience, and improved accuracy—make it a compelling choice for businesses aiming to strengthen their security infrastructure.
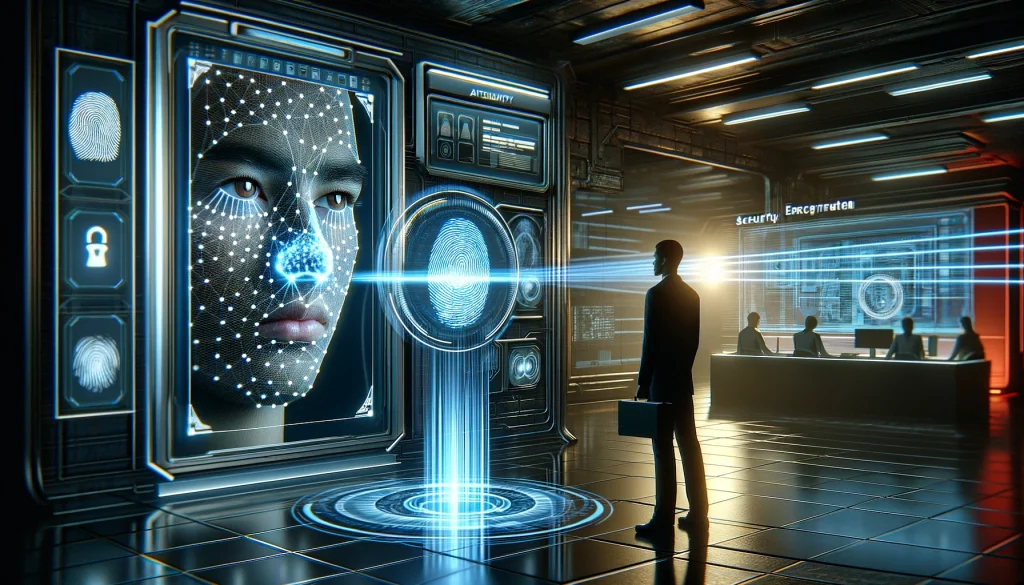
Biometric authentication emerges as a powerful security measure for businesses to protect sensitive information and valuable assets amidst the growing cyber threats in the digital age. This method verifies individuals’ identities using unique physical or behavioral characteristics, such as fingerprints, iris patterns, facial features, voice patterns, and typing patterns. Biometric authentication offers a high level of security by making it difficult for unauthorized access. It eliminates the risk of forgotten or stolen passwords, making the authentication process more convenient and user-friendly.
The adoption of biometric authentication in business environments is driven by its numerous advantages over traditional authentication methods. It provides robust access control, ensuring that only authorized individuals can gain entry, significantly reducing the risk of unauthorized access and identity theft. Biometric authentication also offers operational efficiency, allowing quick and easy access to secure areas or systems without needing physical keys or access cards. Additionally, it enhances data protection by minimizing the chances of data breaches. It ensures compliance with data protection regulations by utilizing unique biometric traits that are challenging to replicate or forge.
Implementing biometric authentication systems, however, comes with challenges such as integration with existing infrastructure, user acceptance, cost, and scalability. Despite these hurdles, the benefits of biometric authentication—enhanced security, increased convenience, and improved accuracy—make it a compelling choice for businesses aiming to strengthen their security infrastructure. Future trends in biometric authentication, such as multi-factor authentication, continuous authentication, and behavioral biometrics, suggest ongoing efforts to enhance security measures and user experience, positioning biometric authentication as a key component of secure and efficient business operations in the digital landscape.


Leave a Reply
You must be logged in to post a comment.