- Due to inadequate cybersecurity measures, SMEs have played a critical role in the global economy and their vulnerability to cyber threats.
- SIEM solutions, which are categorized as commercial and open-source, are pivotal for real-time monitoring and correlating security events across an organization’s network.
- Future research directions include integrating unstructured Open Source Intelligence (OSINT) data, Security Orchestration Automation and Response (SOAR), and Artificial Intelligence (AI) technologies to enhance the capabilities of open-source SIEM systems.
Researchers are addressing the increasing need for robust cybersecurity measures among Small and Medium Enterprises (SMEs) in the face of evolving cyber threats. Given the budgetary constraints and limited cybersecurity expertise in SMEs, their study focuses on the potential of open-source Security Information and Event Management (SIEM) systems as cost-effective solutions. The research evaluates various open-source SIEM solutions, examining their ability to meet modern security challenges and regulatory compliance. Through empirical testing in simulated SME network environments, the study assesses these systems’ performance, resource utilization, and real-time data processing capabilities, offering valuable insights for cybersecurity practitioners and decision-makers in SMEs.
Due to inadequate cybersecurity measures, SMEs have played a critical role in the global economy and their vulnerability to cyber threats. The COVID-19 pandemic has exacerbated these vulnerabilities as remote work environments have become new targets for cybercriminals. SMEs often underestimate the risks and impact of cyber attacks, believing they are only directed at larger organizations. However, data shows a significant percentage of cyber attacks target SMEs, highlighting the need for effective cybersecurity strategies. Adopting defense-in-depth strategies and SIEM systems is recommended for comprehensive security management.
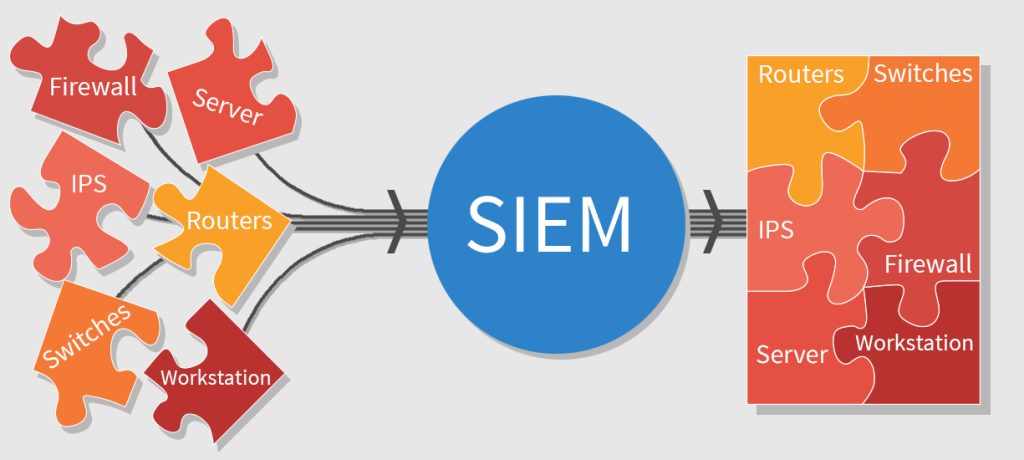
SIEM solutions, categorized into commercial and open-source, are pivotal for real-time monitoring and correlating security events across an organization’s network. While commercial SIEM solutions offer extensive features and support, their high costs make them impractical for many SMEs. Although cost-effective and customizable, open-source SIEM solutions often lack the comprehensive features and support provided by commercial counterparts. The article explores the strengths and limitations of open-source SIEM solutions, aiming to fill the research gap in their detailed security and performance evaluation.
The research methodology quantitatively evaluates shortlisted open-source SIEM solutions, namely Wazuh, SIEMonster, OSSIM, and Elastic Security. These solutions are assessed in a simulated enterprise-grade SME network environment for their event processing capabilities and security features. The study reveals that Wazuh emerges as the best solution regarding security features and performance, making it a suitable choice for SMEs seeking customizable and cost-effective SIEM solutions. However, the article also acknowledges that open-source SIEM solutions, while beneficial, are not yet on par with commercial offerings. Future research directions include integrating unstructured Open Source Intelligence (OSINT) data, Security Orchestration Automation and Response (SOAR), and Artificial Intelligence (AI) technologies to enhance the capabilities of open-source SIEM systems.


Leave a Reply
You must be logged in to post a comment.