- Security Configuration Management (SCM) is an essential cybersecurity practice for ensuring systems are configured correctly to meet security and compliance standards.
- SCM serves dual purposes of enhancing security and ensuring compliance. Misconfigurations are entry points for cyberattacks, making secure configurations critical for reducing breach risks.
- The integration of SCM with other core cybersecurity processes like file integrity monitoring (FIM), vulnerability management (VM), and log management (LM) creates a holistic security approach.
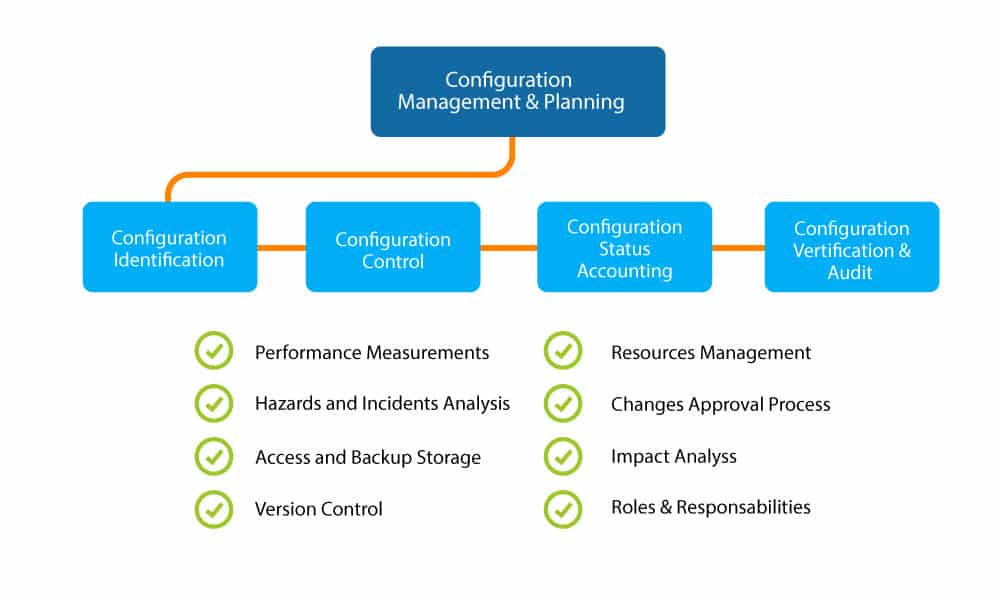
Security Configuration Management (SCM) is an essential cybersecurity practice for ensuring systems are configured correctly to meet security and compliance standards. SCM helps reduce cyber risks by securing configurations, which involves detecting and remediating misconfigurations across both on-premises and cloud environments. Effective SCM minimizes an organization’s attack surface by maintaining system integrity, ensuring configurations do not drift into insecure states over time.
SCM serves dual purposes of enhancing security and ensuring compliance. Misconfigurations are entry points for cyberattacks, making secure configurations critical for reducing breach risks. Organizations can maintain a safe and compliant state by establishing secure configuration baselines and continuously monitoring for deviations. SCM tools facilitate this process, significantly reducing the time and effort required for audit preparation and helping organizations maintain compliance with various regulatory standards like PCI DSS, SOX, and HIPAA.
The integration of SCM with other core cybersecurity processes like file integrity monitoring (FIM), vulnerability management (VM), and log management (LM) creates a holistic security approach. FIM detects unauthorized changes to files and system attributes, providing the necessary data to ensure SCM’s effectiveness. VM helps identify and prioritize vulnerabilities needing remediation, complementing SCM by addressing misconfigurations and vulnerabilities. LM centralizes log data to provide context and improve incident detection and response.
Modern enterprises face challenges like expanding cloud infrastructures and dynamic environments, which complicate SCM. Automated SCM tools must monitor configurations across both on-premises and cloud assets in hybrid environments. This includes managing configurations for DevOps containers and industrial control systems (ICS). Effective SCM requires continuous monitoring and management of configurations, ensuring that all physical, virtual, or cloud-based assets adhere to defined security baselines. This approach helps organizations promptly identify and address configuration drifts, maintaining a robust security posture against evolving cyber threats.


Leave a Reply
You must be logged in to post a comment.